Key Management Policy Template
Key Management Policy Template - This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key. Ensure that reveal consistently follows industry standards for encryption and key management. This policy and standard apply to all reveal. Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able.
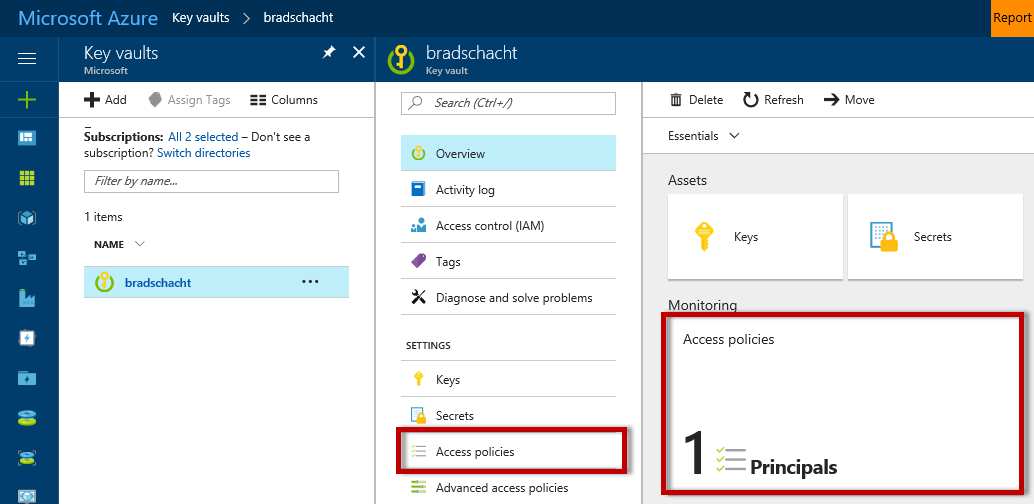
Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. Ensure that reveal consistently follows industry standards for encryption and key management. This policy and standard apply to all reveal. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key.
Ensure that reveal consistently follows industry standards for encryption and key management. This policy and standard apply to all reveal. Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key.
Encryption Key Management Policy Template
This policy and standard apply to all reveal. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key. Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. Ensure that reveal consistently.
Best Account Plan Template
Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key. Ensure that reveal consistently follows industry standards for encryption and key management..
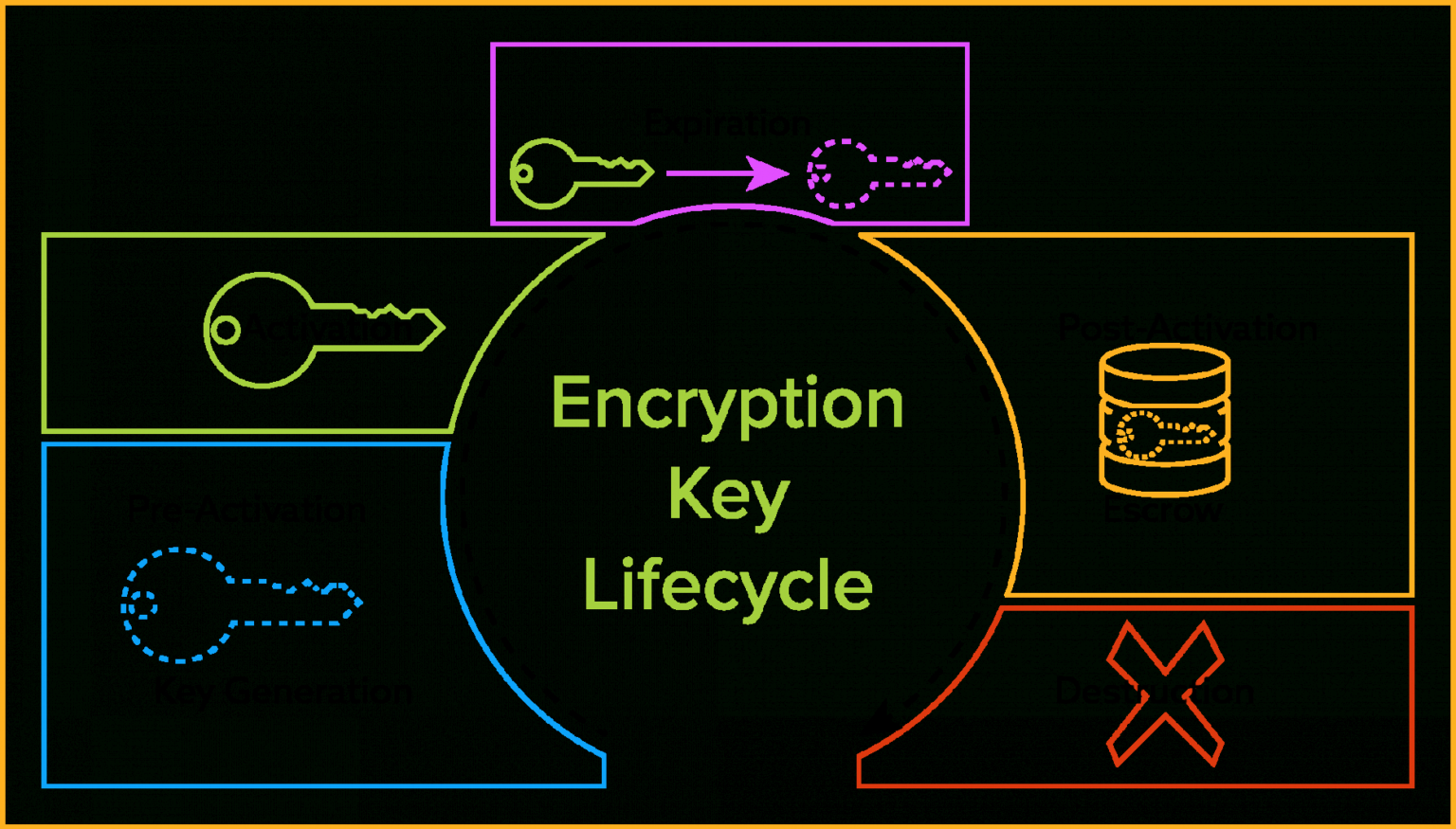
The Definitive Guide To Encryption Key Management Fundamentals
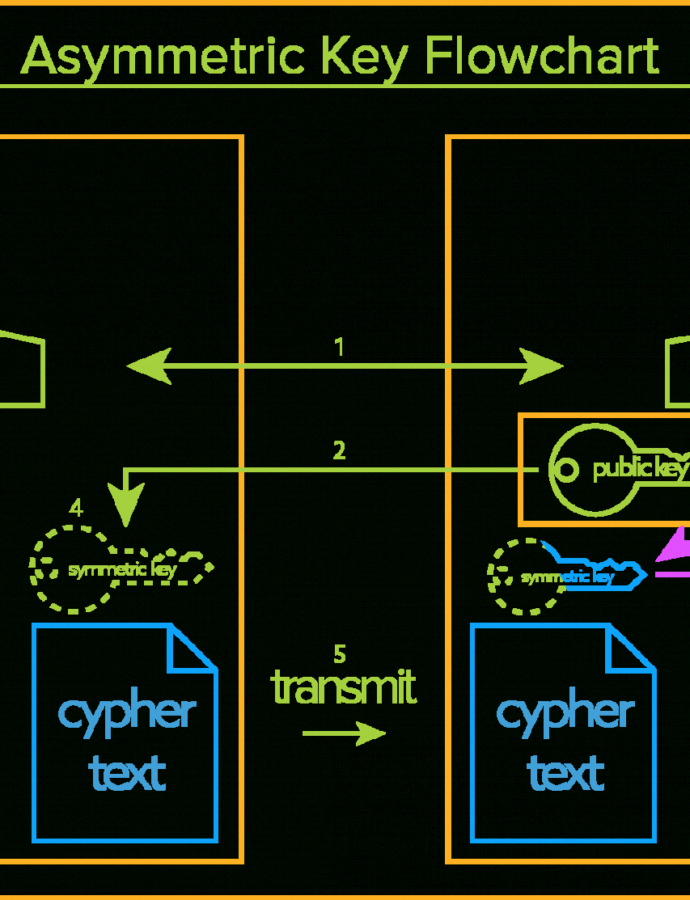
Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. Ensure that reveal consistently follows industry standards for encryption and key management. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key..
Policy Acknowledgement Template
This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key. Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. Ensure that reveal consistently follows industry standards for encryption and key management..
Encryption Key Management Policy Template Policy template, Management
Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. This policy and standard apply to all reveal. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key. Ensure that reveal consistently.
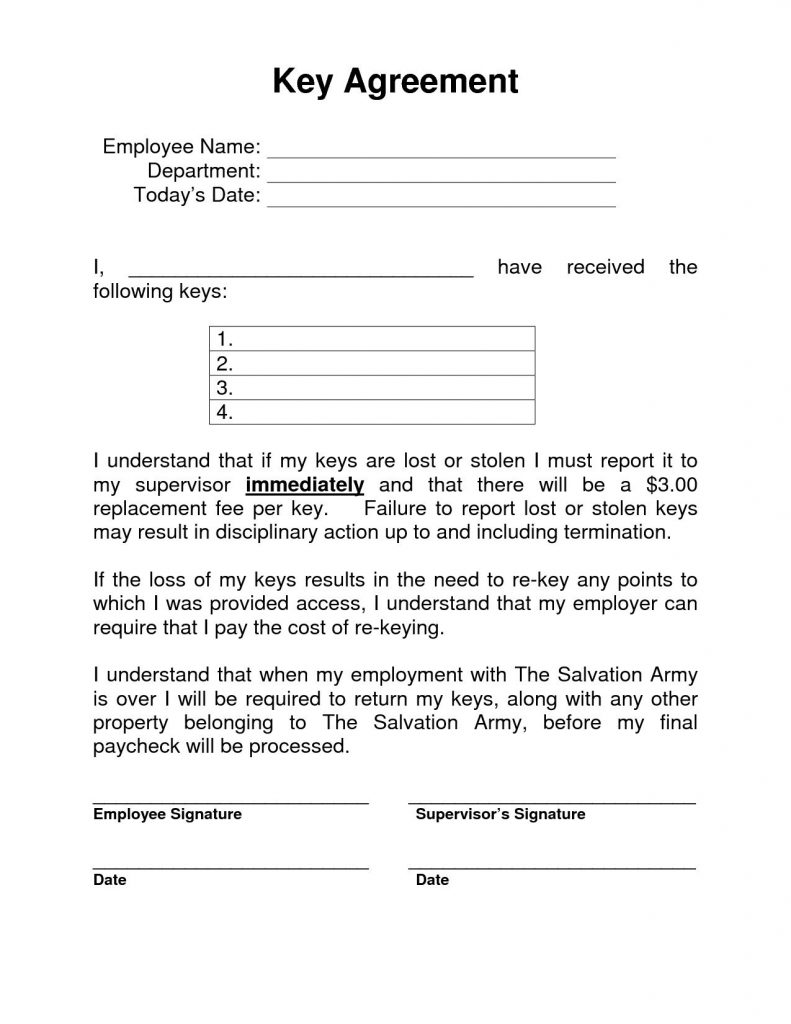
Employee Key Holder Agreement Template 10+ Examples of Professional
Ensure that reveal consistently follows industry standards for encryption and key management. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key. Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able..
ISO 27001 Cryptographic Key Management Policy Template
This policy and standard apply to all reveal. Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. Ensure that reveal consistently follows industry standards for encryption and key management. This policy seeks to implement a proper key control process and then preserve it by.
Printable The Definitive Guide To Encryption Key Management
Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. Ensure that reveal consistently follows industry standards for encryption and key management. This policy and standard apply to all reveal. This policy seeks to implement a proper key control process and then preserve it by.
Encryption Key Management Policy Template
This policy and standard apply to all reveal. Ensure that reveal consistently follows industry standards for encryption and key management. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key. Although it is preferred that no humans can view keys, as a minimum, the key management system.
Best Encryption Key Management Policy Template Sparklingstemware
This policy and standard apply to all reveal. Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key. Ensure that reveal consistently.
This Policy And Standard Apply To All Reveal.
Although it is preferred that no humans can view keys, as a minimum, the key management system should account for all individuals who are able. This policy seeks to implement a proper key control process and then preserve it by restoring security in a timely manner whenever key. Ensure that reveal consistently follows industry standards for encryption and key management.